The American Trucking Associations has joined the Automotive Information Sharing and Analysis Center, a global community that shares information about cybersecurity risks facing connected vehicles.
ATA Aims to Strengthen Trucking Cybersecurity with Alliance
The American Trucking Associations has joined the Automotive Information Sharing and Analysis Center, a global community that shares information about cybersecurity risks facing connected vehicles.

ATA has joined the Automotive Information Sharing and Analysis Center, a global community that shares information about cybersecurity risks facing connected vehicles.
Image via Auto-ISAC
ATA wanted to improve its efforts to develop and promote best practices in cybersecurity to better prepare the trucking industry as vehicles become increasingly connected. The strategic alliance with Auto-ISAC provides additional support and resources to ATA’s existing Fleet CyWatch program through added cybercrime analysis capabilities and response guidance for member fleets.
CyWatch is a member-led program for fleets to report cybercrimes, receive analytic support, and incorporate latest developments on cybersecurity industry issues, alerts, best practices, and national security awareness.
“As digital technology advances and the world grows increasingly connected, it is critically important that we unite America’s passenger and commercial vehicle expertise to combat emerging threats and safeguard key transportation modes,” said Chris Spear, president and CEO of ATA. “This relationship with Auto-ISAC puts us at the cutting edge and, along with ATA’s Fleet CyWatch program, will strengthen trucking’s security posture in the evolving global marketplace.”
In addition to CyWatch, ATA’s Technology and Maintenance Council recently held its inaugural Fleet Data Management and Cybersecurity Conference where TMC unveiled its new Cybersecurity Issues Taskforce. Chaired by Mark Zachos of DG Technologies, the taskforce will ballot the first of several cybersecurity recommended practices to be released later this summer.
“Security is a process. There’s working on awareness, the sharing of information, and conducting penetration testing to find where a company might be vulnerable,” said Zachos. “There is a lot of work to do.”
Related: Can Trucks be Hacked?
More Fleet Management

HDT Q&A: Brian Antonellis on the Growing Need to Replace Old Trucks
Fleet Advantage's Brian Antonellis says it's time for fleets to get back to the fundamentals of good maintenance practices. And that includes replacing older, inefficient equipment.
Read More →
Truckstop.com Adding to Open Deck, Heavy Haul Offerings
Load matching for flatbed, lowbed, oversize and overweight loads can't be automated like basic van freight, but Truckstop.com is adding more high-tech tools to help.
Read More →
Trucker Path, Truckstop.com Expand Load Access Partnership
An expanded Trucker Path and Truckstop.com integration brings more freight opportunities into the TruckLoads app while emphasizing security and network quality.
Read More →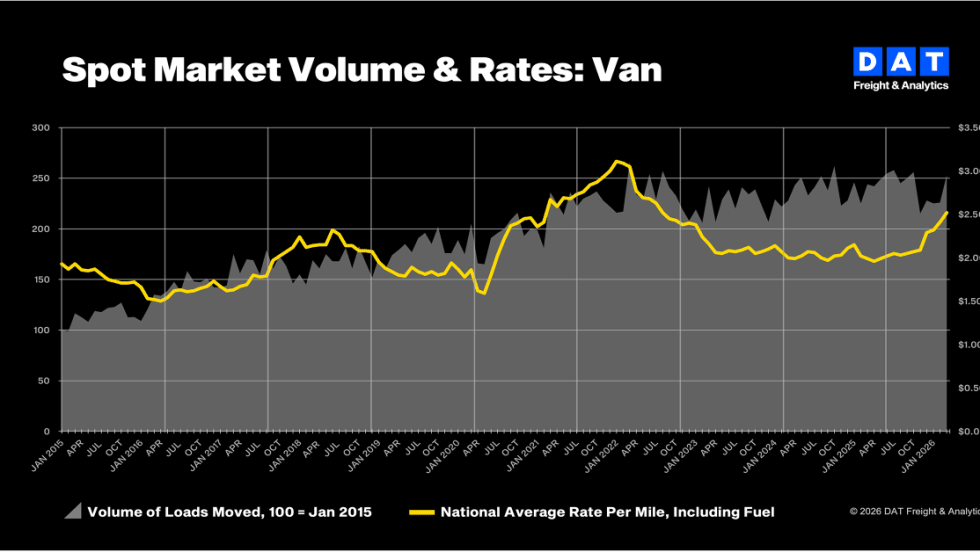
Truckload Rates Hit Two-Year Highs as Diesel Costs Surge, DAT Says
Strong March freight demand combined with a spike in fuel costs pushed both spot and contract truckload rates to their highest levels in more than two years.
Read More →
The AI Conversation You Need to Have with Your TMS Provider
Everyone’s talking about AI — but is your transportation management system actually built for it?
Read More →
Kriska Buys Fellow Canadian Carrier Sharp Transportation Systems
Being part of KTG will allow Sharp to expand and improve its services.
Read More →
Bill in House Would Raise Minimum Insurance for Motor Carriers to $5 Million
The Fair Compensation for Truck Crash Victims Act would increase insurance requirements for interstate motor carriers by nearly seven times.
Read More →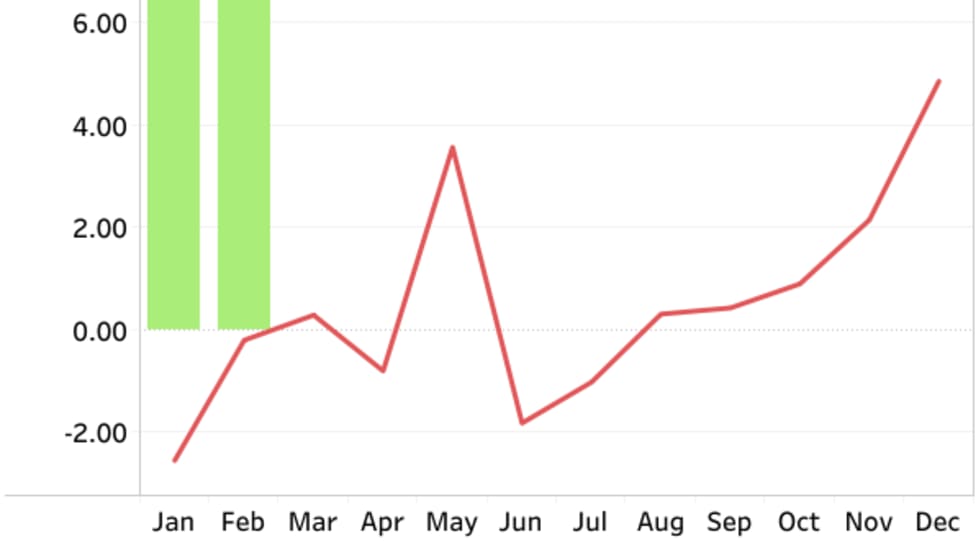
FTR Trucking Conditions Index Hits Four-Year High in February
Strong freight rates push TCI to 10.2, but FTR expects fuel-price volatility to skew March results.
Read More →
C.H. Robinson Offers Carriers Relief as Diesel Prices Surge
C.H. Robinson is waiving fees on fuel cards and cash advances for April and May, aiming to help carriers offset rising diesel costs tied to geopolitical instability.
Read More →
What Trucking Events are Happening in 2026?
Looking for trucking-related conventions, expos, and other events? Heavy Duty Trucking has developed this list of national and larger regional trucking shows and events.
Read More →