Protecting Your Data
Keeping a company’s most vital information safe requires a company-wide effort.

Massive data hacks at large retailers such as Home Depot or Target may get most of the headlines, but smaller companies find themselves victims of hacking or data breaches on an almost daily basis. As a panel at last fall’s American Trucking Associations management conference illustrated, that includes trucking companies.
There, OutWest Express, a 150-truck long-haul fleet based in El Paso, Texas, shared how what looked like a resume attached to a routine truck driver application actually hosted a malicious bit of software, or “malware,” that rampaged through its systems. The company had to pay a lot of money for an outside firm to do a “forensic recovery” of its data. And then it discovered that whoever stole the data was calling OutWest’s brokers, booking loads under its name and insisting on cash advances. But of course, the loads never got picked up.
Businesses need solid procedures and policies in place to protect themselves and their data from these kinds of threats.
“In the IT industry, hacks are a daily occurrence,” says Mike Krut, senior vice president information technology, Penske Truck Leasing. “We’ve built our organization around keeping our customers’ and our data secure.” These efforts are a “large focus” of the company’s senior leadership, he says, “because the integrity of our brand is measured by how well we can protect data.”
Woody Lovelace, senior vice president of corporate planning and development at Southeastern Freight Lines, Lexington, S.C., says “data security is something we look at on an ongoing basis so we do things that fall into best practices. It’s almost a perpetual activity, plugging holes” and educating employees.
Protecting your data goes beyond guarding against fraud.
“Data is the looking glass into the health and profitability of a company,” says Kevin Linardic, vice president technology for software provider Carrier Logistics. “Two things we are most concerned about is [first], keeping that information out of the hands of those who have no business knowing the information, and second, making sure no one can do something that would affect the company’s ability to do business — a hack, in other words.”
A system hack or data security breach doesn’t have to involve theft to have a huge impact on your business.
“A company becomes so dependent on data and technology, if they were to lose access to the data or system for a day or longer, how would that affect their business?” asks Marc C. Tucker, an attorney specializing in data security with the firm Smith Moore Leatherwood, Raleigh, N.C. If a company’s system is down for an extended period, there is a clear financial ramification if you can’t dispatch trucks for several hours or several days.
What types of threats are out there?
There are a variety of ways a company’s system can be compromised, from phishing emails to an internal bad actor to an outside hack. Some companies have had their systems taken “hostage” by hackers who then demand a ransom to bring the system back up. That’s part of what happened to OutWest, but when they called the numbers provided by the supposed ransomers, they didn’t reach anyone.
Scott Bortzel, vice president IT delivery services at Penske, says his company is “seeing a lot of email-delivered malware, or phishing attacks.” Only now, these email attacks have become more sophisticated, what Bortzel calls “spear phishing” — a targeted attack that involves some research by the attacker to find out the name of a senior company executive and then gearing the message toward that person or make it look like it is coming from someone the target knows.
“Any company is a potential target,” he adds, “especially companies that processes credit card transactions.”
Lovelace says the threats SEFL worries most about come from the need to grant people access to the system. “There is a fine line to giving people in the company access to data they need without opening yourself up to piracy or malware. I think the ability of people outside the network to corrupt the files is probably what keeps IT guys up at nights.”
Employees are an important part in a company’s cyber strategy, for better or for worse. “One of the things I say over and over on employees: They can be your strongest link in the chain and they can be the weakest link – it goes both ways,” Tucker says. “It’s the biggest open door for data problems nine times out of 10.”
Policies and procedures
Making sure an employee doesn’t click on the wrong email means establishing and enforcing strict policies regarding network access and data use. That includes significant training, Lovelace says. “When someone comes on they have to be trained on accessing our network. After that is ongoing education.”
While his company’s IT department takes the lead in this area, there are ways end users contribute to maintaining a secure system – the way they use their email, for example. “We put out bulletins to remind people of things they should be doing.”
Another part of a strong policy is limiting access to your system. At Southeastern, not everyone has access to all the parts of the system, Lovelace says. Associates and drivers have access that is specific to their job duties. There is also a formal process of approval for associates to get additional access.
Other steps companies can take include log-in standards, network standards, auditing requirements to check who has accessed what, authorization standards, forced password changes (including mobile devices and in-vehicle computers) and following best practices in terms of firewall, spam filters, etc.
At Penske Leasing, Krut says, in addition to these procedures, everyone signs a code of conduct regarding IT use.
“Keep the doors locked and don’t show people who don’t need access where the key is,” Linardic says. “You give the key only to people who need to get through that door.” Plus, make sure you do regular audits so you know who uses that key.
It’s important that everyone buys into these procedures, from the top down, Tucker says. “Data management and cyber security is not just an IT issue, it’s a company issue. If there is a data breach, it affects the whole company, not just the IT department.”
Use outside consultants
Many companies recommend using security consultants. Outside consultants “help us consider vulnerabilities we may not have considered,” Lovelace says. And even though his company has such expertise in-house, they feel it important to bring in outside help to stay on top of the ever-changing nature of the threats.
Krut agrees that working with third-party security experts is something carriers need to consider. “It gives you a look at new threats and trends you may not be aware of.”
In addition to working with outside experts, it is also important to have a clear plan of action for when a data breach occurs.
“If you think about motor carriers, most carriers have an accident response plan in place,” Tucker says. “If a vehicle is in an accident, they don’t have to think about what to do – they know what to do. They have things set up with their insurance companies, attorneys, adjusters, accident reconstructionists, etc. When preparing for a potential data breach or attach, the same principles apply. When an attack is happening is not the best time to think about what do to. You want to be prepared.”
That means having already invested in cyber insurance (most general insurance policies won’t cover a data breach), for instance, or having outside experts such as attorneys and security experts ready to step in when needed. “You may want a third party consultant ready to come in and analyze the attack, shut it down and then put things back together and do a forensic analysis.”
Legal Ramifications
Along with financial loss and business disruptions, there are also legal ramifications of a data breach that revolve around the notion of data ownership, Tucker says. Companies collect tons of data, and not just about their vehicles. There is also a lot of data on their employees, customers, payments, credit cards – and that’s just the tip of the iceberg. A key issue is who owns all that data.
“Ownership is dictated by who is responsible for the management of that data, who can control access to the data,” Tucker explains. “That translates into responsibility for that data and making sure it is secure.” Along with that ownership also comes responsibility if there is a data breach.
For instance, if a motor carrier has health-related information on employees via a company-supplied health plan, a breach of that data requires (by law) a specific response in terms of what entities are alerted about the breach. If employee social security numbers are hacked, that requires another set of specific responses.
And that extends to third parties that a carrier might share data with. “The way I think about it, is that if you share your data with a third party, you want to hold that third party to the same standards as you hold your company,” Tucker says.
Companies can ensure third parties and others with whom they share data follow the best practices in terms of data security using a contractual warranty that creates a duty or obligation under the contract. Tucker says such a warranty may require a third party to carry cyber insurance to a certain limit.
If using third-party services, Tucker says, make sure you understand the terms of use and the services’ privacy policies, which outline what information is being collected and how it will or will not be used. If you don’t take the time to read the fine print, “you may not realize you’ve agreed to let a third party use your data in some aggregated way.”
Even with solid procedures in place, the cyber threat requires continued vigilance. And that takes more than just the IT department, says Southeastern’s Lovelace. “It’s the responsibility of all of your associates. It’s a shared responsibility.
“The people doing this are very creative and it’s something you have to stay on top of.”
Correction 5/16/16: The original version of this article referred to attorney Marc C. Tucker as Turner and to Penske Truck Leasing's Mike Krut as Kurt. Both have since been corrected.
More Fleet Management

Jamie Hagen Gets Real About Running a Small Fleet in an Uncertain Economy
Small fleet owner Jamie Hagen says new legal risks, volatile fuel prices, and a changing freight market are forcing small carriers to rethink how they operate -- and what they can afford.
Read More →
Jamie Hagen Gets Real About Freight, Fuel Prices, Safety, and Small-Fleet Survival
Running a small trucking fleet right now isn’t easy, especially right now. And Jamie Hagen doesn’t sugarcoat it.
Read More →
Jamie Hagen Gets Real About Freight, Fuel Prices, Safety, and Small-Fleet Survival
Running a small trucking fleet right now isn’t easy, especially right now. And Jamie Hagen doesn’t sugarcoat it.
Read More →
Data Lock‑In or Integration Lock‑Out?
Data fragmentation is costing dealerships, OEMs, fleets, and upfitters millions. Here’s why interoperability may be the fix the trucking industry needs.
Read More →
What Trucking Fleets and Brokers Need to Know About This Supreme Court Case
In May, the U.S. Supreme Court ruled that freight brokers can be held liable for damages if a truck they have contracted with is involved in an accident. Listen as this transportation attorney breaks down the ruling and its implications for the trucking industry.
Read More →
The Trucking Industry’s Threat Intelligence Gap
The trucking industry has no shortage of cybersecurity reports and cargo crime statistics. What it lacks is timely, operational intelligence that fleets can actually use.
Read More →
Truck Crash Rates Are Down. So Why Do Insurance Costs Keep Rising?
ATRI’s latest research points to litigation, social inflation, and soaring claims costs as key drivers behind record-high liability premiums for trucking fleets. But there are things motor carriers can do.
Read More →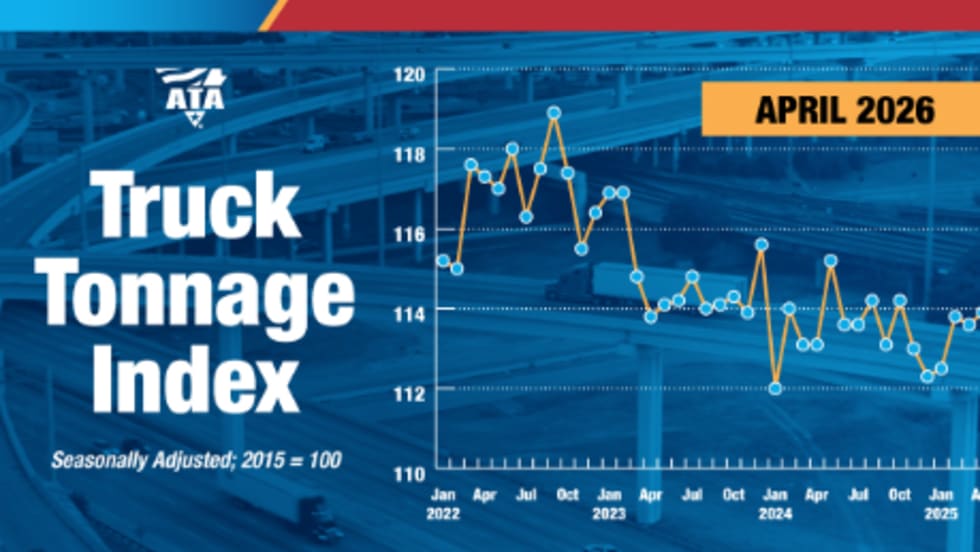
ATA Truck Tonnage Holds Steady in April at Highest Levels Since 2022
ATA’s For-Hire Truck Tonnage Index was unchanged in April after a strong March gain, with freight volumes remaining at their highest levels since late 2022.
Read More →
Fleetworthy Launches Connected Platform for Fleet Readiness Across Safety and Compliance, Toll Management, and Weigh Station Bypass
Fleetworthy has unveiled three major product launches it says mark a new era in fleet readiness.
Read More →
Behind the SCOTUS Broker Ruling Part 1
Transportation attorney Greg Feary breaks down the recent Supreme Court decision that brokers can be held liable for damages in truck accidents and what it means for the trucking industry going forward.
Read More →