For years, cybersecurity awareness training typically consisted of generic warnings about phishing, click-through annual refreshers, and mandatory presentations that were about as exciting as a root canal. These programs were built with the best intentions.
Traditional Cybersecurity Training Doesn’t Stop Today’s Social Engineering Attacks in Trucking. Learn What Does.
Culture, not technology, determines cyber resilience. Learn how trucking fleets can replace ineffective cybersecurity training with real-world, scenario-based awareness programs.

Cybersecurity training that used to provide a one-size-fits-all, generic message is transitioning to targeted, role-based, real-world training.
HDT Graphic
But they missed the mark.
They weren’t designed in line with how people actually work in the trucking industry, or with how real bad actors operate.
Cyberattack strategies using social engineering have evolved significantly over the past several years, with extremely rapid changes seen since the explosion of large language model (LLM) AI tools starting in November 2022 with the release of ChatGPT.
Attacker techniques changed from broad “low-hanging fruit” campaigns to targeted, industry-tailored attacks involving sophisticated lures that are exponentially more difficult to detect with legacy defensive tools.
The most effective awareness training programs in the trucking industry today instead focus on shaping everyday behavior, rather than checking an annual compliance box.
Training that used to provide a one-size-fits-all, generic message is transitioning to targeted, role-based, real-world training that focuses on the actual business processes in the trucking industry and the tactics bad actors use to attack fleets.
Effective social engineering awareness training is less about memorizing abstract red flags and more about creating a culture of awareness and finely tuning employees’ instincts to improve decision-making habits across the organization.
Cybersecurity Training For Different Roles
One of the most important shifts in training approaches is the move toward targeted, role-based training.
A truck driver does not face the same social engineering risks as a billing specialist. A maintenance technician does not have the same threat exposure as a dispatcher.
When awareness training reflects these differences, the result is higher engagement, higher retention, and far better outcomes. A simulation or lesson that mirrors an employee’s real workflow has a much greater chance of influencing their behavior over the long term than a generic warning about the dangers of phishing.
Scenario-Based Cybersecurity Training
In the same way that effective training is tailored to the employee’s role, scenario-based exercises have proven especially valuable.
Successful cybersecurity training programs are moving away from outdated simulations focused on generic consumer scams. Instead they use exercises that model the real communication patterns attackers are using.
These might include “urgent” requests to reroute freight, fake rate confirmations with malicious links or embedded exploits, and fraudulent invoices of overage, shortages and damages (OS&D) claims.
When employees train on identifying threats in the types of messages and documents they actually receive every day, they develop the muscle memory required to use those skills in their roles.
Shortcomings of Traditional Cybersecurity Training
Annual compliance-oriented click-through training has little long-term effect. How do we know? The same attack techniques keep working!
Employees return to their routines and quickly forget material that is abstract and general, disconnected from their actual responsibilities.
Overly simplified training that asks employees to identify threats based on poorly written emails, obvious “badguy.com” fake hacker domains, and clunky gift card scams miss the mark entirely.
Exposing employees to realistic attack patterns and role-specific, scenario-based exercises using industry-appropriate phishing lures dramatically raises functional social engineering awareness.
More frequent training exercises and concise, targeted training modules that fit into normal daily workflows are critical to a successful social engineering awareness program.
Training data should also provide feedback that is incorporated into business processes to inform things like how pickup certification processes should be handled, or what safeguards would most effectively prevent unauthorized banking information changes.
The Psychology of Social Engineering
Cybercriminals rely on predictable human behaviors for social engineering attacks.
They exploit urgency, authority, routine, and trust. These attack angles are especially effective in trust-dependent, high-tempo environments, such as dispatch and customer-facing operations teams, and in dispersed and remote workforces, such as drivers and work-from-home employees.
A driver already running late is more susceptible to a fraudulent delivery location change. An overworked dispatcher may quickly approve a request that, at first glance, appears to come from a familiar broker domain.
Attackers study these behaviors and deliberately craft scenarios that create pressure, capitalize on distractions, or trigger an emotional response.
Protecting Against Social Engineering Cyberattacks
Effective awareness training acknowledges these psychological principles and works with them rather than against them.
People remember what feels relevant and clearly connected to their responsibilities. They engage more fully when exercises mirror situations they’ve actually faced.
Perhaps most importantly, they are more likely to adopt better security habits and behaviors when training doesn’t just focus on what the attackers are doing but addresses the why behind the success of those methods.
Shame-based approaches are bad for business. Training programs should focus on rewarding positive behaviors rather than punishing less desirable behaviors. When employees fear negative consequences, they are more likely to hide mistakes or make assumptions instead of asking questions. This is another tendency that attackers regularly exploit.
Choose the carrot over the stick when it comes to training and building a culture of cybersecurity awareness. An organization that normalizes reporting and encourages the questioning of any deviation from expected patterns allows incidents to surface quicker and prevents a small issue from snowballing into a major setback.
Reinforcing a Cybersecurity Culture
Starting at the top, most mature organizations treat cybersecurity awareness as a central business function, not a separate security compliance requirement.
Training is simply a part of workflows, onboarding, and both performance and operational review cycles. Leadership actively reinforces security awareness and consistently promotes safe behavior rather than focusing on yearly compliance requirements. They model cybersecurity awareness in their own actions.
This matters because culture, not technology, is what determines how resistant an organization is to social engineering in the real world.
An organization with a strong security culture standardizes how data is handled, how sensitive instructions are confirmed, how identities are verified, how process changes are communicated, and crucially, how exceptions are escalated and addressed.
Employees internalize the expectation that security is everyone’s responsibility, and leadership at every level of the organization models this expectation visibly.
When cybersecurity awareness becomes part of the organizational culture, training becomes much more than a dry educational exercise or a compliance checkmark. It becomes a precision instrument that supports the success of the organization.
The Road Ahead for Cybersecurity Training in Trucking
Cyberattacks exploiting social engineering are evolving, and awareness training must evolve with it.
The investments in awareness training for your teams that you make today will directly reduce fraud exposure, cyber-enabled cargo theft, and the likelihood of a successful ransomware attack on your organization far into the future.
Practical, role-specific training builds confidence and sharpens the instincts of everyone on the team.
Combined with building a strong reporting culture, where exceptions are flagged quickly, and employees are recognized and rewarded for asking one more question when something doesn’t seem quite right, or enforcing one more verification step when a supposed identity just feels a little off, results in a stronger and more resilient organization.
All these actions build a culture of “see something, say something.” If your “spidey” senses are tingling...there is probably a reason why.
Social engineering remains a dominant trend in cybersecurity. Keep an eye out for NMFTA’s annual Trucking Cybersecurity Trends Report in December, which will touch on this important topic and other trends that trucking and supply chain professionals need to be cognizant of in the new year.
More Fleet Management

'Beyond Compliance,' Regulations, Driver Coaching on ATRI’s 2026 Research List
The American Transportation Research Institute will examine driver coaching, regulatory impacts — including the "Beyond Compliance" concept —and weather disruptions that shape trucking operations.
Read More →
HDT Q&A: Brian Antonellis on the Growing Need to Replace Old Trucks
Fleet Advantage's Brian Antonellis says it's time for fleets to get back to the fundamentals of good maintenance practices. And that includes replacing older, inefficient equipment.
Read More →
Truckstop.com Adding to Open Deck, Heavy Haul Offerings
Load matching for flatbed, lowbed, oversize and overweight loads can't be automated like basic van freight, but Truckstop.com is adding more high-tech tools to help.
Read More →
Trucker Path, Truckstop.com Expand Load Access Partnership
An expanded Trucker Path and Truckstop.com integration brings more freight opportunities into the TruckLoads app while emphasizing security and network quality.
Read More →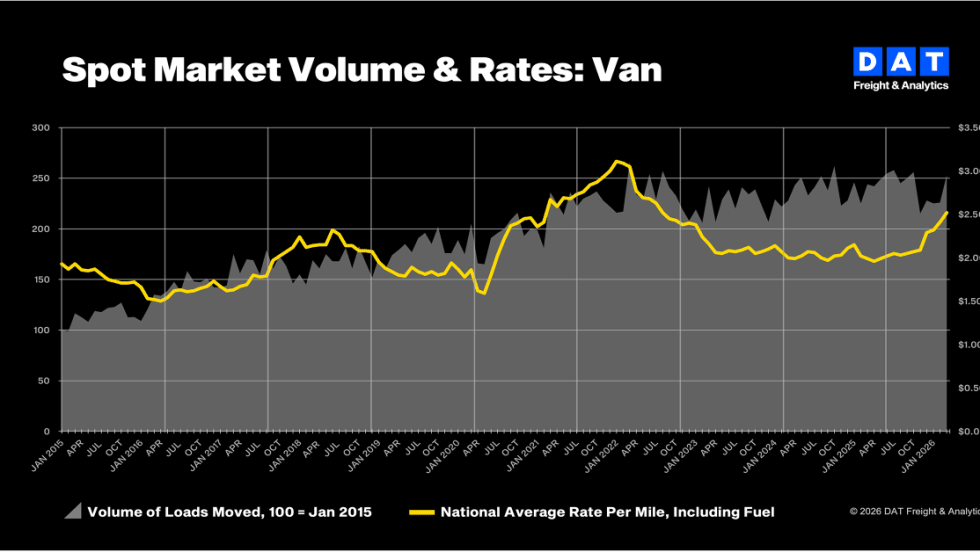
Truckload Rates Hit Two-Year Highs as Diesel Costs Surge, DAT Says
Strong March freight demand combined with a spike in fuel costs pushed both spot and contract truckload rates to their highest levels in more than two years.
Read More →
The AI Conversation You Need to Have with Your TMS Provider
Everyone’s talking about AI — but is your transportation management system actually built for it?
Read More →
Kriska Buys Fellow Canadian Carrier Sharp Transportation Systems
Being part of KTG will allow Sharp to expand and improve its services.
Read More →
Bill in House Would Raise Minimum Insurance for Motor Carriers to $5 Million
The Fair Compensation for Truck Crash Victims Act would increase insurance requirements for interstate motor carriers by nearly seven times.
Read More →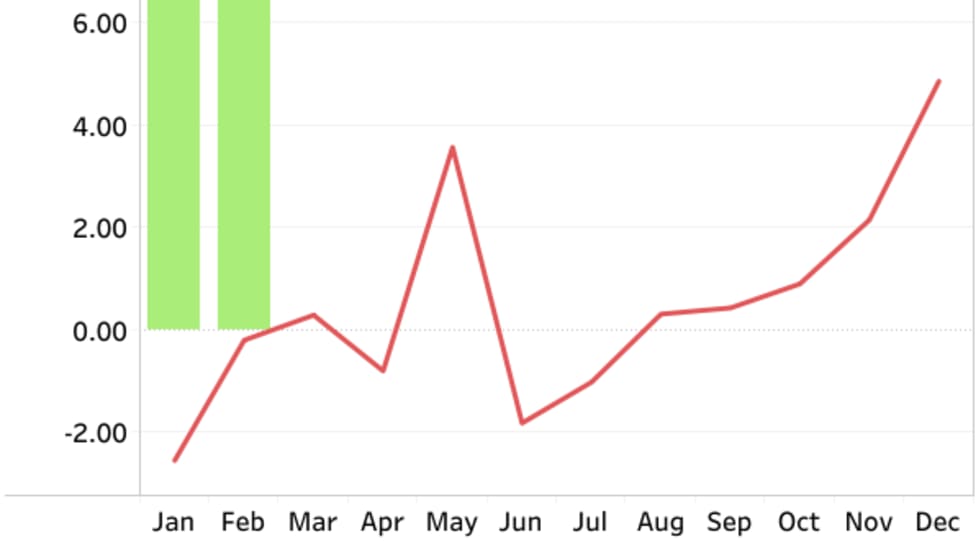
FTR Trucking Conditions Index Hits Four-Year High in February
Strong freight rates push TCI to 10.2, but FTR expects fuel-price volatility to skew March results.
Read More →
C.H. Robinson Offers Carriers Relief as Diesel Prices Surge
C.H. Robinson is waiving fees on fuel cards and cash advances for April and May, aiming to help carriers offset rising diesel costs tied to geopolitical instability.
Read More →