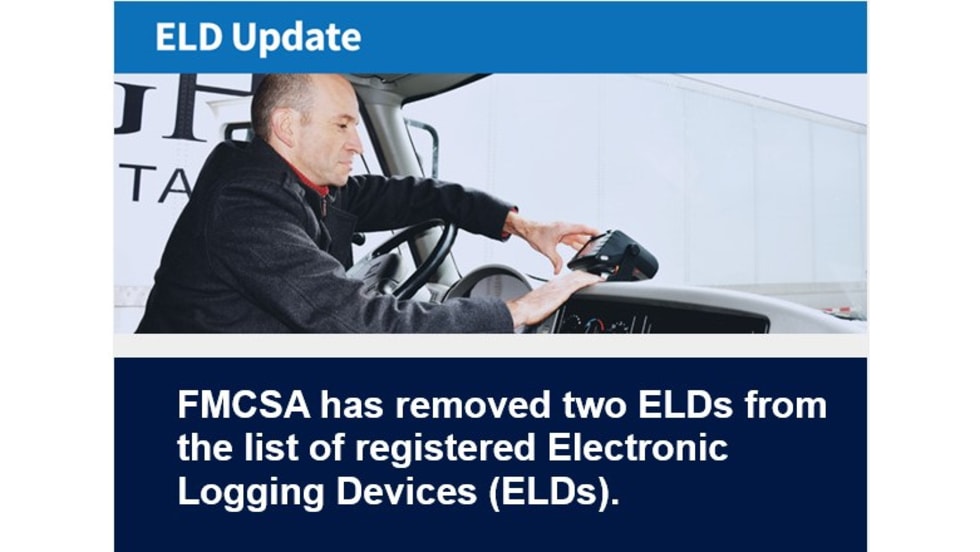
The University of Tulsa is partnering with a group of vehicle cyber security industry organizations to develop a hardware device that will prevent the hacking of heavy trucks through hacked electronic logging devices.
A group of faculty and students from TU’s department of mechanical engineering are joining the consortium of organizations led by the nonprofit National Motor Freight Traffic Association to increase the protection of electronic logging devices through the use of a Controller Area Network Data Diode hardware device.
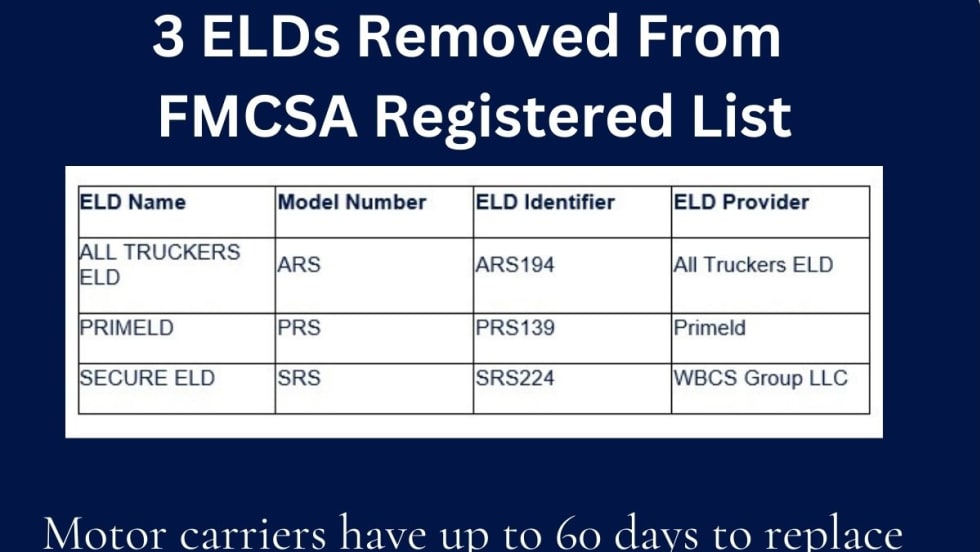
The CAN Data Diode would provide security to a truck by preventing communication from an ELD to a commercial vehicle. By isolating the ELD from a truck’s own connected systems, it would act as a hardware safeguard against hacked third-party ELDs.
“The CAN Data Diode will help carriers comply with mandatory ELD regulations while also protecting onboard vehicle networks that could be compromised by a cracked ELD,” said Jeremy Daily, TU associate professor whose technology designs the CAN data diode is based on.
Hackers may target certain ELDs that lack basic cyber security safety measures and use it as an entry point to critical systems on a truck. The CAN Data Diode solves this potential security threat by eliminating all possible communication to the vehicle network from the ELD device and restricting data from the vehicle to only devices that meet the ELD mandate.
The CAN Data Diode project is a low-cost network isolation solution for commercial vehicle operators who cannot afford sophisticated fleet management applications to keep their vehicles secure from mandated ELDs.
“The work we do at TU with our industry partners should help reduce the risk of cyberattacks in heavy vehicles on today’s roads,” said Daily. “We look forward to working with our partners to continue development and real-world implementation for the CAN Data Diode.”